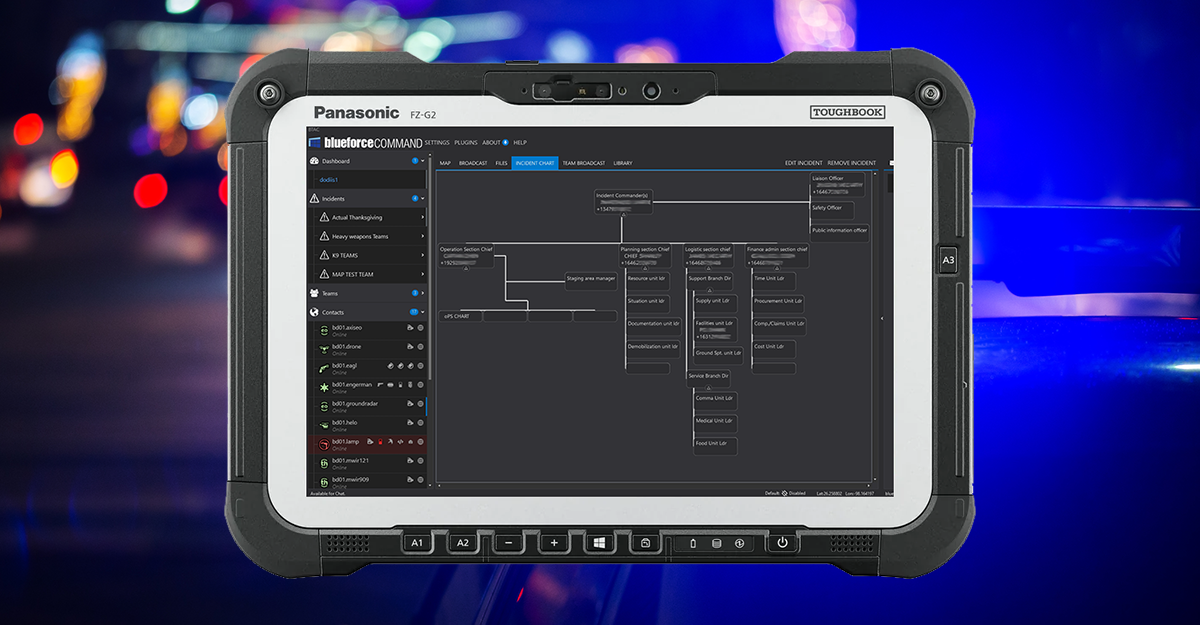
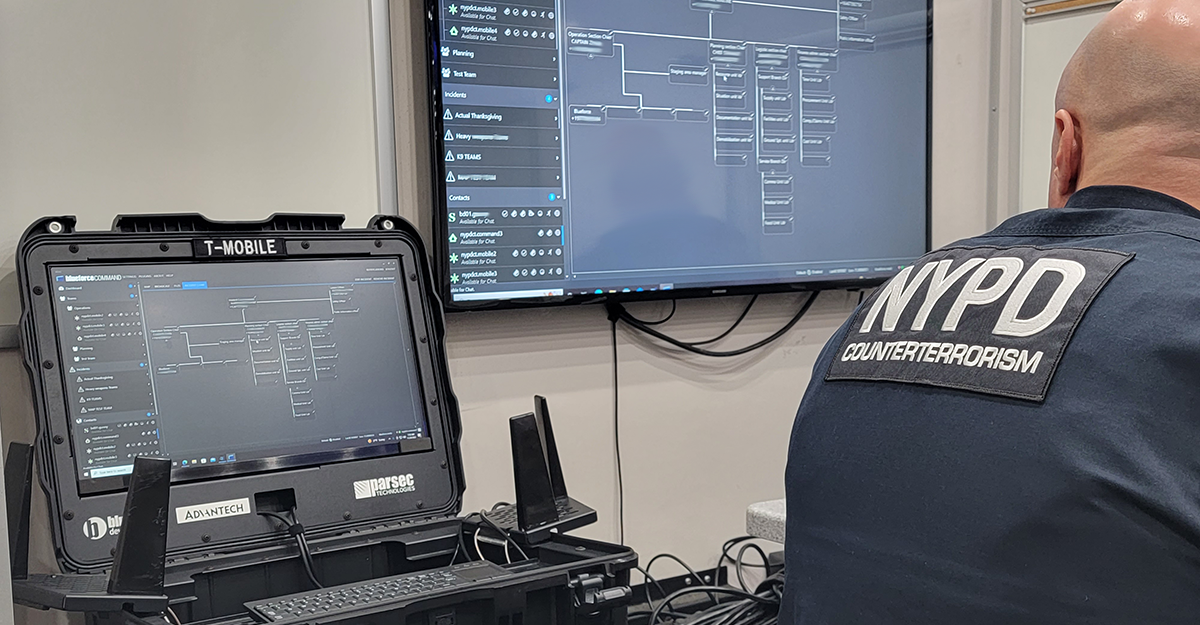
Virtual ICS Checkin: New Capability for Adaptive ICS Module for BlueforceCOMMAND
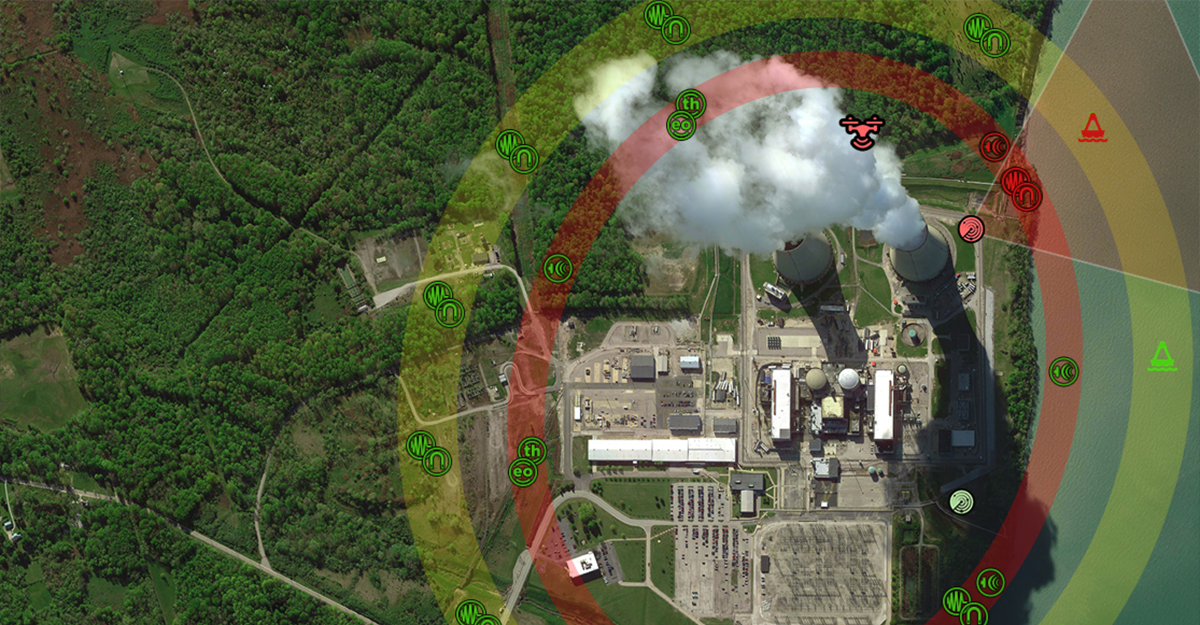
The Incident Command System (ICS) is a standardized, on-scene, all-hazards incident management concept. It was developed in the 1970s by firefighting agencies in the United States as a means of effectively managing incidents involving multiple agencies and organizations. The ICS provides a common structure and terminology for incident management and is designed to be scalable, so that it can be used for incidents ranging from...
Read More