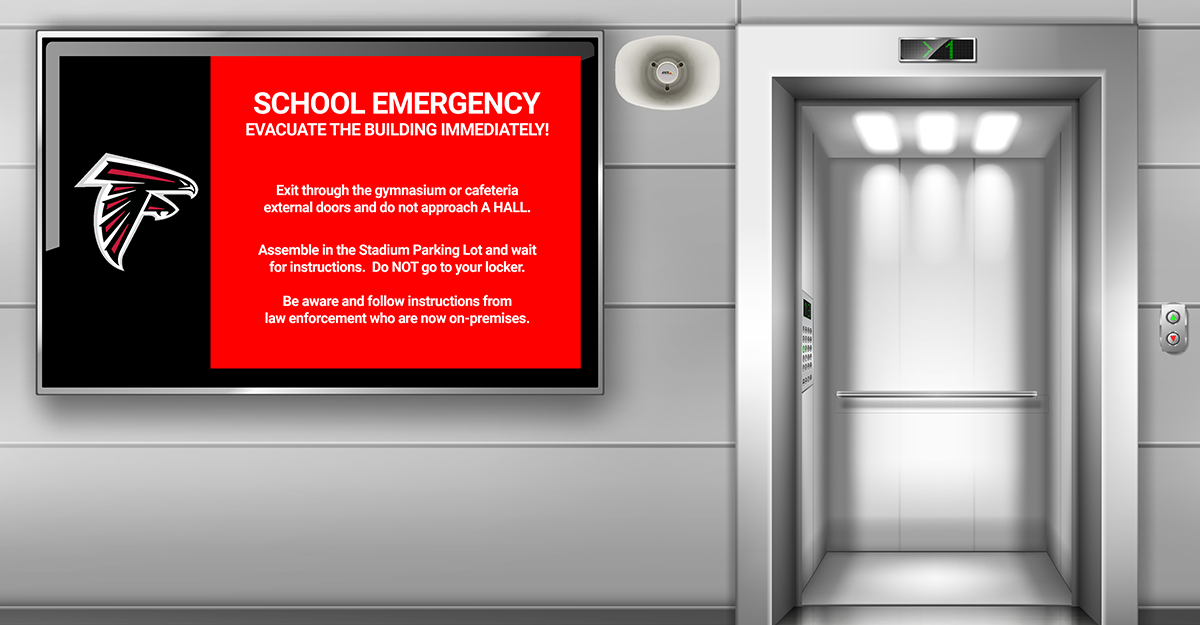
Force protection (FP) is a multi-dimensional pursuit, incorporating many operational concepts including prescribed personnel TTPs and multiple technology areas. The scope of facility-based FP spans a wide spectrum of activities directed toward the protection and management of personnel, assets, facilities and real property, crossing multiple functional, organizational and security domains. Security, surveillance, and intrusion detection are integrated into force protection, but their resources and infrastructure...
Read MoreThe 2022 Blueforce Texas Road Show
The 2022 Blueforce Texas Road Show gives you hands-on access to the latest in Public Safety, Safe Campus, and Autonomous Platform technologies. The Road Show kicks off Tuesday October 11, 2022 in Houston. For more information, click here…